When you’re setting up a new site, migrating, or upgrading your brand’s existing website, it’s understandable that website security may not be the first thing that comes to mind.
With so many tasks to juggle to get your site up and running, it’s easy for security considerations to take a back seat.
However, here’s the unfortunate truth: small- to mid-sized businesses, including startups, have every reason to be just as concerned about security as globally operating enterprise brands.
This blog post will discuss protecting your site, security threats, and the importance of siding with secure web hosting.
- Why Sites Get Hacked
- How Security is Typically Compromised
- The Best Servers for Website Security and Keeping Data Safe
- Shared Responsibility – How Data Centers Reinforce Website Security
- Common Website Security Features and Security Concerns
- Keeping Your Website Security Threats at Zero
While headlines often highlight data breaches that target well-known brands like Target and Sony, the reality is that startups and small operations often fly under the radar of news coverage. The statistics paint a slightly different story from the media.
In fact, a staggering 43% of cyber attacks are aimed at small businesses, including network breaches, website code injection, compromised mobile applications, and more.
And when website and network security are breached, it can take most businesses an average of 197 days to detect it.
A lot of damage can be done in that time frame, which is why cybercrime losses continue to increase. According to data from Trustwave, roughly $600 billion is lost annually.
Even if you operate a less complex website, don’t assume you’re safe from threats. eCommerce sites, in particular, handle secure consumer data, making them lucrative targets for hackers. However, traditional business websites should also be aware of the risks as they may still use plugins or applications that handle basic user information, including login credentials.
The 2018 Trustwave Global Security report found that 100% of web applications tested displayed at least one security vulnerability, with 11 vulnerabilities as the median number per app. Remember, your website is a digital storefront and the gateway to your brand’s reputation, customer trust, and financial well-being.
Why Sites Get Hacked
A staggering number of websites fall victim to hacking incidents yearly. Some attacks may happen randomly without specific targets, but it’s important to note that targeted attacks are also widespread.
A select few may target a specific enterprise brand or government website for the challenge or over a matter of hacktivism (related to religion, nationalism, anti-globalism, human rights, etc., where public-facing content is defaced). But, in most cases, the websites they choose to hack are random.
Hackers use scripts that broadly search websites for common vulnerabilities in virtually every case. And, unless they’re specifically looking for a challenge, they’re more likely to take the least challenging vulnerabilities to gain quick access.
Modern web hosts are stepping up to provide all this. They’re enabling plug-and-play experiences where businesses can integrate AR-powered virtual try-on solutions directly into their websites without having to hire an army of developers. By providing retailers with tools to embed realistic, 3D try-on capabilities for things like glasses, makeup, hats, earrings, and more, they let businesses of all sizes jump into AR without building everything from scratch.
Apart from finding vulnerabilities in a website, hackers also push malicious code in various ways, like through email or by leaving comments on your WordPress site. For that purpose, the safest approach for small businesses and people who take security seriously is to use an advanced email service that is very low-cost.
This ensures that your incoming emails are scanned and delivered promptly, while advanced filtering protects your business from malicious actors.
“Over the past three years, more than 3/4 of websites scanned contained unpatched vulnerabilities,” according to a Symantec study, “one in seven (15%) of which were deemed critical in 2015.”
When they scan for vulnerabilities, they aren’t making distinctions between the size or age of the business.
So many small businesses are likely to stick out and become targets because small business owners don’t typically prioritize security. They also don’t have the budget to maintain an IT division capable of regular monitoring or maintaining updated, secure systems, unlike large enterprise brands.
According to Chris Eggleston, most hackers look for three things when they attack a website:
- High-jack your SMTP server. They upload a script that uses your relay server to send spam emails to hundreds of emails daily until your hosting provider shuts down the relay server.
- High-jack your website traffic. They will redirect traffic coming from search engines to their money-making websites. These sites will be branded with your colours and logo so that visitors think they’re in the right place.
- Distribute malware. Have you ever visited a website to have a message pop up that says you need to update your Flash player, and when you click on it, you end up with a virus on your computer? That is one way that the virus gets delivered from hacked websites. But thankfully, Flash player has been discontinued in favour of more modern web technologies like HTML5.
Understanding how security is compromised and what hackers are looking for gives a better view of the security technologies used by hosting providers and what you can do to improve the security of your own website.
How to Use Proxies for Secure Social Media Automation
Using proxies successfully in social media automation demands a mix of using the right tools and following best practices to assure security and effectiveness. However, you need to get a trustworthy proxy provider like Marsproxies.
How Security is Typically Compromised
Security vulnerabilities are common among web applications. If you think you’re in the clear with web application security, though, you should check the apps you use to do business, especially those integrated with your website. An example of web applications small business owners use includes:
- Web analytics tools
- Writing and grammar applications and plugins
- SEO plugins and applications
- Email integration apps
- Third-party social integration applications
- Productivity applications
- Communication applications like chat and contact forms
And a vast selection of others, each with the potential for vulnerabilities that could compromise your website security.

Here are some of the most common vulnerabilities in websites:
- SQL injections: Injection of code that grants access to or corrupts database content, allowing the attacker to read, write, or otherwise alter data.
- Cross-site scripting: XSS allows attackers to run scripts in your browser that can hijack the browsing session, alter website content, and redirect the user to any chosen destination.
- Broken authentication: Poor session management and broken authentication make it easy for hijackers to take over an active user session and assume the user’s identity. Session cookies are the most unique method for these attacks.
- Misconfigured security: When security misconfigurations occur, a hacker or hijacker can access all manner of private data or features up to and including a completely compromised website or network.
While these are some of the more common vulnerabilities, there’s a lot more that can happen. Thankfully, there are also numerous ways reputable website hosting companies actively work to keep your website and the hosting servers safe from hijacking and intrusion.
The Best Servers for Website Security and Keeping Data Safe
While the concept of web hosting is simple – a company grants you space to store files and data displayed to the public as a website – it can become a bit more complex when you start dealing with the security of your data.
Hosting companies indeed make a great deal of effort to ensure servers and websites remain secure. However, there’s a fine line between where your responsibility for web security ends and where the responsibility of the website hosting company begins.
Selecting the Best VPN for Savings
Free VPNs might look tempting, but they can be slow, have fewer server choices, and offer weaker security. Paid ones are faster, more reliable, and keep your data safer, making them a better option for saving money and staying secure online. To maximize your savings and protect your data, choosing a reliable alternative like CometVPN is crucial.
That can change depending on the hosting environment you choose.

Website Security and Shared Hosting
Shared hosting is the most common hosting platform for many startup websites and small businesses. They’re more cost-effective and easy to set up. One reason for the cost savings is the website hosting company grouping a number of websites on a single server.
Hence the name “shared.”
This shared setup has continued to fuel myths calling the platform an insecure hosting environment. Truthfully, shared hosting is a solid and affordable option for many people hosting anything from personal hobby sites to business websites. As long as you work with a reputable host that understands website security, you have little to worry about – at least on the host’s side.
Now if you’re looking for more security options on shared web hosting, we recommend stepping up to a higher tier plan which also brings additional security measures and a fully managed Web Application Firewall – simply known as WAF.
You not only get access to a real-time malware scanner, but you also get automatic backups.
Website Security and Virtual Private Servers (VPS)
VPS environments are often favoured when it comes to security. Still, if you look closely at those favouring VPS, it’s typically the IT crowd, like professional network administrators. VPS hosting can be more secure than a typical shared hosting plan or self-hosted website, but only if you have the budget to invest in someone with the technical knowledge.
Without a knowledgeable, reliable system administrator (or a good working knowledge of your own), you can open yourself up to many more vulnerabilities with a VPS.
The benefit of VPS is that they offer far more security options and variations in configuration – but that’s only useful if you know what you’re doing.
Shared Responsibility: How Data Centers Reinforce Website Security
Data centers are essentially the technology backbone for web hosting companies. These locations exist worldwide, with many companies operating their own or leasing space within multiple data centers.
Data centers can range from small operations with minimal infrastructure and space due to small server needs (think small enterprise with a virtual private network) to massive warehouse structures with rows of servers (Google’s data centers and Amazon Web Services come to mind).
And when you store a significant quantity of hardware, processing and managing a perpetual flow of personal and proprietary business data, certain steps are necessary to keep everything safe and secure, not only from malicious code but on a physical level too.
While the site owner is responsible for their designated space within a server, the data center goes to great lengths to manage the servers’ physical (and digital) security and safety. This includes:
- Environment controls that keep equipment operating at a safe temperature. A room full of electronics will generate a significant amount of heat which can damage components if they’re not kept cool.
- Backup power supplies that keep servers operating, even when the power grid goes down, for unexpected reasons. These keep servers running and guarantee uptime until power is restored.
- Surveillance systems for monitoring the interior and exterior of the data center as well the activity of everyone on site.
- Metal detectors and weight monitors in server access rooms to ensure hardware doesn’t enter or exit without approval.
- Mantrap rooms that use a combination of biometrics, security access, single-entry doors (one person at a time), guards, and surveillance to ensure access is limited to the data center (Google uses similar security, and fewer than 1% of employees ever see the inside of the data center).
- Server cages are used within data centers to enclose and protect specific servers or groups of servers, segregating sensitive data and equipment from non-sensitive data. These cages sometimes include CCTV surveillance for additional monitoring.
- Architectural security is often considered in construction to reinforce the facility itself, which can often include bulletproof glass, severe weatherproofing, vehicle-restricted buffer zones, high-impact crash barriers, and extensive fire suppression systems.
Data centers take physical security seriously to dramatically mitigate the security risk of physical attack, damage, and possible threats on site. But that still leaves the question of the most common and obvious threats and vulnerabilities to website security: hacking and software-based attacks.
Here’s how website hosting companies and data centers work to keep you safe on the digital front.

Common Website Security Features and Security Concerns
When choosing a hosting provider, remember that no single security feature will make your hosting platform any more secure than the next.
Instead, it’s the cumulative protection provided by a wealth of features that contribute to your website’s highest level of security.
These are the features you ideally want to be offered and some core security concerns that should be addressed by the hosting provider.
Firewalls (Software and Hardware)
Firewalls are software (or hardware) designed to monitor and filter activity before it reaches the web server. When configured, a set of rules is created and applied to all incoming and outgoing traffic in order to protect the systems and data.
Firewalls work through one or more methods, including filtering (analyzing all data being passed through the firewall against a set of filters), inspection (inspecting incoming data to a site against a database of trusted information where approved data passes), and proxy (captures unapproved or bad traffic before it hits your site).
It’s common for a single firewall to be configured to apply to an entire server with shared hosting, so individual hosting accounts have virtually no control over firewall configuration.
It’s possible with some hosting plans to upgrade to a dedicated firewall, which would let you create specific rules dictating who can (and cannot) access your website.
Data Backup, Restore Points and Redundant Hardware Backups
Even with carefully managed site content, any manner of incident, including a malicious attack, could lead to data loss. It’s ideal to find a website hosting company with a selection of options for backups.
Automated and manual data backups are standard for virtually every web hosting company, providing a rolling backup of the site’s current version. In addition to those backups, a string of restore points gives you a point of jumping back to a prior version well before a breach occurred – useful if it’s been some time since an intrusion.
Redundant hardware backups are extra server banks carrying a mirror of the current versions of live servers. They’re integrated so that the traffic can be instantly routed to a redundant backup in the event of a server failure to avoid downtime and data loss.
Sandbox Development
Performing any kind of update or site maintenance can leave your entire website vulnerable to attack, especially if you’re installing and testing new applications or making adjustments to a script. A sandbox or dev environment allows you to test all changes in a live (but not public-facing) environment rather than making changes directly to the files accessible to the public (and potential hijackers/bots).
When working with WordPress, another way of having a sandbox of your website is installing it locally to your computer – a topic we deeply discussed in another blog post.
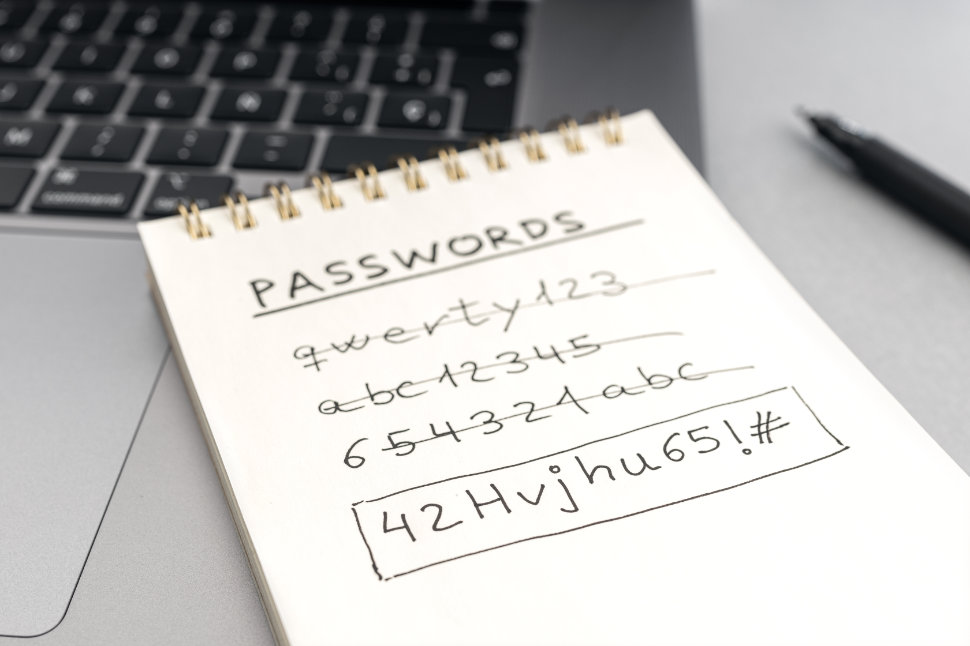
User Access and Password Controls
It’s common for hosting platforms using software like cPanel to offer various levels of user access control and password management. Since these user accounts give various levels of access to the core files of your website, they should be reserved for your team members.
Depending on the nature of your site, you may also have user access set up for customers, subscribers, and guest authors, each with their own private passwords to gain access. Since website users can vary from simple content posting rights to unrestricted file access, you’ll want to set the bare minimum permissions required for any of them, with user access reviews ensuring verification of these permissions.
It’s a good rule of thumb to create a password policy depending on the types of accounts you create and the number of other users. For example, accounts that can have far more impact on your site’s operation and public-facing appearance should have stricter guidelines and stronger password requirements.
You should consider using a password manager for all user accounts to improve website security, especially if you’re working with multiple employees or contractors with access to your website. A password manager eliminates manual password creation, often resulting in employees choosing weak passwords or reusing passwords across multiple platforms and accounts.
The primary benefit of a password manager is the ability to generate strong, complex passwords while storing those in an encrypted vault.
Your website hosting company may provide or recommend a password manager. If not, several trusted applications are available that are secure and won’t store password data in the cloud – which should be generally avoided.
User access and passwords are the client’s responsibility, so careful and regularly monitoring user accounts is as important as the initial configuration.
Data Encryption and SSL Certificates
SSL certificates are a key part of eCommerce and, after recent updates to Google’s Chrome browser, a much larger part of safe browsing as a whole.
These certificates are small data files that are registered and bound to a domain and the organization’s details. When activated and configured on a website, it activates the HTTPS protocol (as opposed to HTTP), establishing a secure connection between the server and the user’s browser.
Through that secure connection, all data is encrypted, especially sensitive information like consumer credit card data, personal contact information, proprietary files, and more. While SSL certificates aren’t required for most websites, Google’s Chrome browser has begun displaying warning messages that a site isn’t secure if the website includes any kind of form to submit data without a legitimate SSL certificate.
For eCommerce sites, SSL is a necessary security component. Not only does it ensure the encryption of sensitive information, but it’s also required for PCI compliance, a requirement of merchant processing companies if you want to accept credit card payments online.
Google has stated that a secure website with appropriate encryption (an SSL certificate) is now a ranking factor. That means part of Google’s core algorithm used to determine the visibility of your website in search includes whether or not your site has a valid SSL certificate. Without one, it’s possible for a website with an SSL (like a competitor’s website) to outrank you in search engines.

DDoS Protection
DDoS, or Distributed Denial of Service, is a method to send an overwhelming volume of traffic/data to a website in the shortest time possible. This data overload prevents the server from processing incoming traffic and can take an unprotected website or server offline.
A reputable and reliable hosting provider will provide documented DDoS protection. With this protection in place, the server can monitor and filter DDoS traffic so that all subsequent hits from the DDoS attack are captured and rejected from the server. In contrast, other legitimate traffic is allowed to pass through normally.
Content Delivery Networks
Content Delivery Networks (CDN) are the invisible backbone of the web and are used to deliver content at much faster rates, particularly across large distances. For example, if you have a website hosted on a server stationed in the U.S., it would take significantly more time for a user in the UK to load your website clearly across the Atlantic compared to another U.S. consumer just a few cities or states away.
Content Delivery Networks are set up around the world, caching website content and offering a volume of benefits to website owners, including:
- Greatly improved page load times, especially for international traffic
- Improved load processing since traffic is split among the CDN rather than all traffic hitting the main server
- Localized coverage in other countries without additional hosting costs
- Reduced bandwidth consumption thanks to improved load processing
As far as website security, CDNs also provide an additional layer of protection against DDoS attacks. Your website hosting provider may provide CDN services in partnership with other providers, and you also have the option of setting up your own CDN access directly with 3rd party CDNs.
Brute Force Detection
A brute force attack is a method hackers use to gain access to a server through an authentic login with legitimate access. Rather than try to locate vulnerabilities, the attackers will use automated software that runs through a massive number of consecutive guesses (username and password combinations) in an attempt to gain access.
Hosting providers typically offer brute force detection to monitor these types of rapid username/password combination submissions. You can also take steps at the user level to help prevent brute force attacks, mainly through better password control.
Strong, lengthy passwords with a high variation in letters and numbers can be extremely helpful.
Some applications or plugins can be installed into content management systems like WordPress, limiting the number of login attempts permitted. Other precautions that may be available beyond detection include:
- Lockouts after forgotten password attempts
- Increasing the amount of time an account is locked out
- Locking individual user accounts
- Preventing your site from revealing when a username is valid in login errors
- Automatically blocking attempts to register or login as specific usernames if they don’t exist, like ‘admin’ or ‘info’
Multifactor Authentication (Two Factor Authentication or TFA)
Multifactor authentication is the process of increasing the steps required to log in, where those additional steps involve tightly controlled applications for verification. In the ideal setup, only the original account owner for a specific username would have access to the second level of authentication.For example, a website administrator has two-factor authentication configured on a site. Any time they attempt to log in with their username and password, the system will generate a text message sent to the mobile phone on record for that user. That administrator then needs to provide the unique access code generated for that session only to gain access to the dashboard.

Virus Protection
Web servers work similarly to a home computer; both use an operating system to run. And just like a home computer, a web server (and the sites/files on the server) are susceptible to attack from viruses and malware. While some can be relatively harmless, most viruses and malware are developed with malicious intent and designed to spread far and fast.
Thankfully, antivirus and malware scanning has become standard for most website hosting companies.
Ideally, you want a hosting provider performing daily/regular antivirus scans and active monitoring like the Protection Power security suite. If possible, find out if scans can be run manually and, if infected files are found, what are the next steps in removal. Your hosting provider may offer a support plan that involves removing malware, though cleaning infected files may fall on the site owner’s responsibility (you).
Keeping Your Website Security Threats at Zero
While your web hosting provider and data centers put in a great deal of effort and expense to keep your data secure, it’s clear that some of the responsibility falls on you to ensure your data (and the private data for your customers) remains secure.
Recapping the above, once you’ve chosen the best website host for your site, here’s a rundown of what you should do to improve protection:
Update your software: Whether you have a custom site or a content management system like WordPress, you must keep all scripts and software up to date. Patches often address security concerns found in older versions and leave your site vulnerable to attack if you fail to update. Ensure plugins, extensions, applications, shopping carts, and templates are included in regular updates and site maintenance to reduce vulnerabilities.
Create a password policy: A strong password policy is key to avoiding intrusion from brute force attacks. Your policy should address a number of factors, including the length and complexity of passwords (10 characters, letters and numbers, special characters, caps), how often passwords are changed/updated (i.e. every 90 days), how passwords are stored (especially with mobile devices), etc. Make sure this password policy is strictly maintained throughout your business.
Use domain privacy: While domain privacy may not seem like a critical security issue, the less information an attacker has, the better. Domain privacy masks the whois data for a website, including personal contact information and location data, all of which could be used maliciously. In addition, you can use infatica.io to safeguard your privacy because your data is encrypted end-to-end.
Install anti-virus software: Your local computers should all be equipped with anti-virus software to protect your data and website. This software can prevent malicious programs like keyloggers and trojans from giving hackers access to your business systems where proprietary information is stored.
Audit your site for vulnerabilities: Since websites often feature custom code in various forms, performing regular audits on your site is a good idea. This doesn’t need to be done manually. There’s no shortage of software and tools online that can be used to scan your website for vulnerabilities. However, it’s advisable to only use the best security scanning tools to keep your organization secure. Remember that no tool is 100% reliable; the best approach to security audits is to work with a professional who can provide a detailed review of your site and explain the steps you need to take to secure your website.
Do manual backups: Reputable website hosting companies provide automated backups, but never trust the system to secure your data. Create a schedule for regular manual site data backups, including databases. Your hosting provider should offer an option to create manual backups within your hosting control panel. Once you have a schedule created, be sure to stick to it.
Use AVS and CVV: For eCommerce websites, you want to take every extra step to maximize security, especially regarding consumer data. Be sure to include an Address Verification System (AVS) and Credit Verification Value (CVV) fields in your checkout. With AVS and CVV, fraudulent attempts are far less likely to succeed since the purchaser must have complete address information and the code on the backside of the credit card to complete the purchase.

Final Words
In today’s digital landscape, where sneaky hackers lurk in the shadows, the size of your website doesn’t determine your vulnerability to cyber threats.
Whether you’re running a small blog or managing an online store, the truth remains: hacks, hijacks, and intrusions can strike at any moment, posing a significant risk to your valuable traffic, customer data, and connections with other users. Every website, regardless of its scale, is a potential target.
To fortify your digital fortress, it’s crucial to make informed choices when selecting a hosting provider.
Look for a partner offering a platform and a comprehensive suite of security features designed to safeguard your online presence. From advanced firewalls and intrusion detection systems to robust encryption protocols, the right hosting provider can be your first line of defence against malicious attacks.
But don’t stop there.
Securing your website is a proactive journey, demanding constant vigilance and the implementation of best practices. Backing up your website regularly ensures you have a reliable copy to restore and minimize downtime, even in the face of a data breach or other website security issues.
Investing time and effort into website security protects your business and instils trust in your visitors and customers. They will feel confident sharing their information, making purchases, and engaging with your brand, knowing that you prioritize their security and privacy.
So, ask yourself: Do you have a comprehensive website security strategy? Have you taken the necessary steps to safeguard your online assets?